In the ever-evolving world of social media, one seemingly harmless action can have severe consequences. Opening a direct message on Instagram may appear innocuous, but lurking behind the screen lies a potential threat.
Hackers are employing increasingly sophisticated tactics to gain unauthorized access to Instagram accounts, leaving users vulnerable to potential cyber attacks.
This article delves into the dangers of opening Instagram DMs, explores the techniques employed by hackers, and provides proactive measures to protect your account and ensure a sense of belonging in the digital realm.
Key Takeaways
- Opening Instagram DMs can lead to unauthorized access to accounts.
- Users can unknowingly engage with malicious links or phishing attempts.
- Hackers employ social engineering techniques to manipulate users.
- Measures such as two-factor authentication, regular password updates, and caution with suspicious links can help protect Instagram accounts from hacking and identity theft.
The Dangers of Opening Instagram DMs
Opening Instagram DMs can pose significant risks to personal privacy and online security. Users may unknowingly engage with malicious links or phishing attempts, which hackers often exploit to gain access to their accounts and personal information. These malicious actors send messages with enticing offers or urgent requests, tricking users into clicking on harmful links or providing sensitive information. Once a user falls victim to these tactics, hackers can gain unauthorized access to their account, potentially compromising personal data and exposing the user to further cyber threats.
In the next section, we will explore some common tactics used by hackers in Instagram DMs and discuss preventive measures to ensure your online safety.
Common Tactics Used by Hackers
Hackers employ a variety of tactics to gain unauthorized access to systems and data. Social engineering techniques, such as impersonating trusted individuals or organizations, are often used to manipulate users into revealing sensitive information.
Phishing email scams, where fraudulent emails are sent to trick recipients into clicking on malicious links or providing login credentials, are another common tactic.
Additionally, hackers may employ keylogging and spyware to secretly monitor and record keystrokes, enabling them to gather confidential information.
These tactics highlight the importance of being vigilant and implementing robust security measures to protect against cyber threats.
Social Engineering Techniques
Social engineering is a psychological manipulation technique used by cybercriminals to exploit human behavior and gain unauthorized access to sensitive information or systems. This tactic preys on individuals’ trust, curiosity, and willingness to help others.
Common social engineering techniques include phishing, pretexting, baiting, and tailgating. Phishing involves sending deceptive emails or messages to trick individuals into providing their personal information or login credentials.
Pretexting involves creating a false identity or scenario to gain trust and extract sensitive information. Baiting involves offering something desirable in exchange for sensitive information or access.
Tailgating involves following someone into a restricted area by exploiting their trust.
To protect against these techniques, individuals should be cautious of unsolicited messages, verify identities before sharing information, and be aware of their surroundings.
Phishing Email Scams
During a phishing email scam, individuals may unknowingly provide sensitive information to cybercriminals through deceptive messages or attachments. Phishing emails are designed to appear legitimate, often mimicking reputable organizations or individuals to trick recipients into divulging personal or financial information. These scams can have serious consequences, including identity theft, financial loss, and compromised cybersecurity.
To protect yourself from phishing scams, it is important to be vigilant and follow these proactive steps:
- Be cautious of emails requesting personal information: Legitimate organizations will never ask for sensitive information via email.
- Verify the sender’s identity: Check the email address and domain to ensure it matches the official contact information.
- Avoid clicking on suspicious links: Hover over links to view the destination URL before clicking.
- Install and regularly update security software: This can help detect and block phishing attempts.
Keylogging and Spyware
The prevalence of keylogging and spyware poses a significant threat to individuals’ privacy and security online. Keylogging is a method used by cybercriminals to record every keystroke made on a device, allowing them to capture sensitive information such as passwords, credit card details, and personal messages. Spyware, on the other hand, is a type of malicious software that secretly monitors and gathers information about a user’s online activities without their knowledge or consent.
These digital threats can be introduced to a user’s device through various means, including malicious email attachments, infected websites, or even through social engineering tactics. Once installed, keyloggers and spyware can track a user’s online behavior, steal personal information, and compromise their online accounts.
To protect against keylogging and spyware, individuals should employ robust cybersecurity measures, such as using strong, unique passwords for each online account, regularly updating software and operating systems, and being cautious when clicking on links or downloading files from unknown sources. Additionally, using reputable antivirus software can help detect and remove any malicious software that may be present on a device.
How Hackers Gain Access to Instagram Accounts?
Hackers can gain access to Instagram accounts through various means. One common method is through phishing email scams, where hackers send deceptive emails that trick users into revealing their login credentials.
Weak password vulnerabilities also provide an entry point for hackers, as they can exploit easy-to-guess passwords or reuse passwords from compromised accounts.
Additionally, social engineering techniques, such as impersonating trusted individuals or manipulating users into revealing sensitive information, can be employed to gain unauthorized access.
It is crucial for users to be aware of these tactics and take proactive measures to protect their Instagram accounts.
Phishing Email Scams
By disguising themselves as legitimate entities, cybercriminals trick unsuspecting individuals into revealing sensitive information through phishing email scams. Phishing emails are designed to appear as if they are coming from a trusted source, such as a bank, social media platform, or online retailer, in order to deceive the recipient into providing login credentials, financial information, or other valuable data. These scams have become increasingly sophisticated, making it difficult for users to detect their fraudulent nature.
To protect yourself from falling victim to phishing email scams, follow these proactive steps:
- Be vigilant and skeptical of emails that request personal information or financial details.
- Verify the sender’s email address by checking for any misspellings or inconsistencies.
- Avoid clicking on suspicious links or downloading attachments from unknown sources.
- Regularly update and maintain strong, unique passwords for all your online accounts.
Weak Password Vulnerabilities
One of the key factors contributing to the vulnerability of Instagram accounts is the use of weak passwords, which can be easily cracked or guessed by malicious actors. Weak passwords, such as common words, personal information, or simple combinations, are vulnerable to brute-force attacks or dictionary-based hacking techniques.
It is crucial to understand that a strong and unique password is the first line of defense in protecting your Instagram account from unauthorized access. To enhance the security of your Instagram account, it is recommended to use a password manager to generate and store complex passwords.
Additionally, enabling two-factor authentication adds an extra layer of protection by requiring a verification code in addition to your password. By taking these proactive measures, you can significantly reduce the risk of your Instagram account being compromised and ensure the safety of your personal information and online presence.
Social Engineering Techniques
The implementation of social engineering techniques, such as phishing and pretexting, remains a significant concern in the realm of Instagram account security. Cybercriminals are constantly finding new ways to exploit users and gain unauthorized access to their accounts.
To protect yourself from these threats, it is important to be aware of the following:
- Phishing: Be cautious of suspicious emails or messages that ask you to provide your login credentials or other personal information. Always verify the source before clicking on any links or sharing sensitive data.
- Pretexting: Attackers may impersonate someone you trust to trick you into revealing personal information. Be skeptical of unexpected requests for information or money, and always verify the identity of the person before sharing any sensitive details.
- Education: Stay informed about the latest social engineering techniques and educate yourself on how to recognize and respond to them. Regularly update your knowledge to stay one step ahead of cybercriminals.
- Strong Security Measures: Implement strong passwords, enable two-factor authentication, and regularly review your privacy settings to ensure maximum protection for your Instagram account.
Signs That Your Instagram Account Has Been Hacked
If you notice any suspicious activity, such as sudden changes in your profile or unauthorized posts, it is crucial to take immediate action as these signs may indicate that your Instagram account has been hacked.
In today’s digital age, where social media platforms like Instagram have become an integral part of our lives, the security of our accounts is of utmost importance. Hackers are constantly evolving their techniques to gain unauthorized access to personal information, and Instagram is no exception.
By being vigilant and recognizing the warning signs of a hacked account, you can protect yourself and your online presence. Some common signs include receiving password reset emails that you didn’t request, discovering unfamiliar email addresses or phone numbers linked to your account, or noticing a sudden increase in spam messages or suspicious activities on your profile.
If you encounter any of these signs, it is recommended to change your password immediately, enable two-factor authentication, and report the incident to Instagram for further investigation. By taking proactive steps, you can safeguard your Instagram account and maintain a sense of belonging in the online community.
Steps to Take if Your Instagram Account Is Hacked
When your Instagram account is hacked, it is crucial to act swiftly and follow the necessary steps to regain control and secure your personal information.
Here are four steps to take if your Instagram account is hacked:
- Change your password immediately: Start by resetting your password to something strong and unique. Avoid using common passwords or personal information that can be easily guessed.
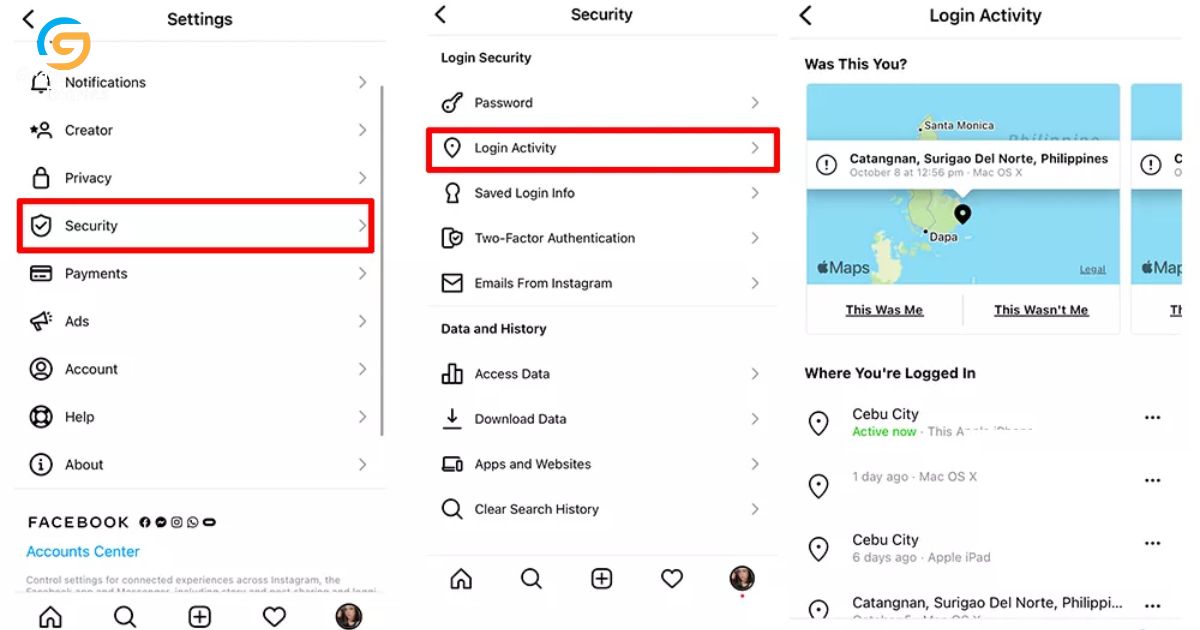
- Enable two-factor authentication: This adds an extra layer of security by requiring a verification code in addition to your password when logging into your account. It helps prevent unauthorized access even if your password is compromised.
- Review your account settings: Check for any suspicious activity or changes made by the hacker. Look for unfamiliar email addresses, phone numbers, or connected apps and revoke access if necessary.
- Report the hack to Instagram: Inform Instagram about the hack by reporting it through their official channels. They will investigate the issue and provide further assistance in regaining control of your account.
Preventative Measures to Protect Your Instagram Account
Implementing effective preventative measures and staying vigilant are key to safeguarding your Instagram account from potential security breaches.
With the increasing popularity of Instagram, it has become a prime target for hackers and cybercriminals looking to gain unauthorized access to personal information and exploit it for their own gain.
To protect your account, it is crucial to follow some best practices. Firstly, enable two-factor authentication to add an extra layer of security. This will require a verification code in addition to your password when logging in.
Secondly, be cautious of suspicious links or messages, as they may lead to phishing scams or malware downloads.
Additionally, regularly update your Instagram app and operating system to ensure you have the latest security patches.
Lastly, consider using a strong and unique password and avoid sharing it with anyone.
The Role of Two-Factor Authentication in Account Security
Enabling two-factor authentication significantly enhances the security of user accounts, as it requires an additional verification step beyond just a password. This added layer of security provides users with peace of mind and helps to prevent unauthorized access to their accounts.
Here are four reasons why two-factor authentication is crucial for account security:
- Protection against password breaches: Two-factor authentication reduces the risk of password breaches by adding an extra layer of verification. Even if a hacker manages to obtain a user’s password, they would still need the second factor, such as a unique code sent to the user’s phone, to gain access.
- Defense against phishing attacks: Two-factor authentication can protect against phishing attacks, as it requires the user to input a unique code or confirm their identity through a trusted device. This prevents hackers from accessing accounts even if they have obtained the user’s credentials through phishing techniques.
- Mitigation of identity theft: By implementing two-factor authentication, users can significantly reduce the risk of identity theft. It adds an extra layer of verification, making it harder for cybercriminals to impersonate users and gain unauthorized access to their accounts.
- Enhanced security for sensitive information: For accounts that contain sensitive information, such as financial or personal data, two-factor authentication is essential. It provides an additional barrier to protect this valuable information from unauthorized access, adding an extra level of security and peace of mind.
Best Practices for Handling Suspicious DMs on Instagram
One should always exercise caution and remain vigilant when dealing with suspicious direct messages (DMs) on Instagram in order to ensure the safety and security of their account.
Instagram has become a popular platform for communication, networking, and sharing content. However, it is important to be aware of potential risks and take necessary precautions.
Suspicious DMs may contain phishing attempts, malware, or links that lead to compromised websites. To protect your account, it is recommended to refrain from clicking on unfamiliar links or providing personal information to unknown sources.
Additionally, enabling two-factor authentication, regularly updating your password, and keeping your device’s software up to date are essential security measures.
Staying Vigilant: Keeping Your Instagram Account Secure
Users must remain cautious and actively monitor their Instagram account to ensure the security of their personal information and prevent any potential breaches. With the increasing number of cyber threats, it is crucial to adopt best practices to protect our online presence.
Here are four key steps to help you stay vigilant and keep your Instagram account secure:
- Enable two-factor authentication: This adds an extra layer of security by requiring a verification code in addition to your password when logging in.
- Regularly update your password: Choose a strong, unique password and update it periodically to minimize the risk of unauthorized access.
- Be cautious of suspicious links and messages: Avoid clicking on unknown links or responding to unsolicited messages, as they may be phishing attempts to gather your personal information.
- Monitor account activity: Regularly review your account for any suspicious activity, such as unrecognized login attempts or unexpected changes to your profile settings.
Frequently Asked Questions
Can Hackers Access My Instagram Account by Simply Opening a Dm?
Hackers can potentially access Instagram accounts through various methods, including exploiting vulnerabilities in direct messages (DMs). It is crucial to stay vigilant, keep software updated, and practice safe online behavior to minimize the risk of being hacked.
What Are Some Common Signs That Indicate My Instagram Account Has Been Hacked?
Some common signs that indicate your Instagram account has been hacked include sudden changes in profile information, unauthorized posts or messages, unfamiliar followers or activity, and difficulty logging in. Stay vigilant and report any suspicious activity immediately.
How Can I Prevent My Instagram Account From Being Hacked?
To prevent your Instagram account from being hacked, it is important to take proactive measures. This includes regularly updating your password, enabling two-factor authentication, being cautious of suspicious links, and using security features such as login alerts.
What Steps Should I Take if My Instagram Account Has Been Hacked?
If your Instagram account has been hacked, take immediate action to secure it. Change your password, enable two-factor authentication, review your connected apps, and report the incident to Instagram for further assistance.
Is Two-Factor Authentication Effective in Securing My Instagram Account?
Two-factor authentication is an effective method in securing your Instagram account. By adding an extra layer of security, it reduces the risk of unauthorized access and potential hacking incidents.
Conclusion
In conclusion, opening a DM on Instagram can potentially lead to your account being hacked if you are not cautious. It is important to be aware of the common tactics used by hackers and to take preventative measures to protect your account.
One interesting statistic to note is that approximately 81% of hacking-related breaches are due to weak or stolen passwords. By implementing two-factor authentication and following best practices for handling suspicious DMs, you can help ensure the security of your Instagram account.